Openssl Generate Private Key No Password
The following instructions will guide you through the CSR generation process on Nginx (OpenSSL). To learn more about CSRs and the importance of your private key, reference our Overview of Certificate Signing Request article. If you already generated the CSR and received your trusted SSL certificate, reference our SSL Installation Instructions and disregard the steps below.
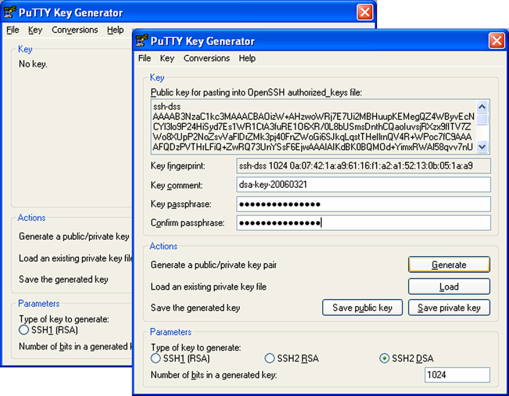
Vultr mac generate ssh key. (I am a fresh learner on SSH and linux OS, sorry.) I can't visit the VPS by code'ssh root@45.32.60.227' on my MAC os Terminal. The following part is the outcome: IT IS POSSIBLE THAT SOMEONE IS DOING SOMETHING NASTY! Someone could be eavesdropping on you right now (man-in-the-middle attack)! It is also possible that a host key has just been changed. Adding an SSH key to your control panel. Once you're logged in, go to Click 'Add SSH Key'. Enter a descriptive name for the key. Paste in your SSH public key. This is a long string beginning with 'ssh-rsa'. You should have saved this from when you generated your key. Click 'Add SSH Key'. Now, when you're deploying servers you will be able to select which SSH keys you want to add to. When accessing a remote server such as a Vultr VPS, it is recommended to use SSH with PKE (Public Key Exchange) which uses a key-pair where the public key is provided to the server and the private key in stored on your machine. SSH Keys can be automatically added to servers during the installation process by adding your public keys in the Vultr control panel. Deploy high performance SSD VPS on the worldwide Vultr network in 60 seconds. Sign up for free and start hosting virtual servers today! We are simplifying the cloud.
In some circumstances there may be a need to have the certificate private key unencrypted. To remove the private key password follow this procedure: Copy the private key file into your OpenSSL directory (or you can specify the path in the command line). A certificate.crt and privateKey.key can be extracted from your Personal Information Exchange file (certificate.pfx) using OpenSSL. Follow this article to create a certificate.crt and privateKey.key files from a certificate.pfx file.
- The following instructions will guide you through the CSR generation process on Nginx (OpenSSL). To learn more about CSRs and the importance of your private key, reference our Overview of Certificate Signing Request article. If you already generated the CSR and received your trusted SSL certificate, reference our SSL Installation Instructions and disregard the steps below.
- How to Generate & Use Private Keys using OpenSSL's Command Line Tool. These commands generate and use private keys in unencrypted binary (not Base64 “PEM”) PKCS#8 format. The PKCS#8 format is used here because it is the most interoperable format when dealing with software that isn't based on OpenSSL.
- Sep 11, 2018 After you have downloaded the.pfx file as described in the section above, run the following OpenSSL command to extract the private key from the file: openssl pkcs12 -in mypfxfile.pfx -out privatekey.txt –nodes. Where mypfxfile.pfx is your Windows server certificates backup. This command will create a privatekey.txt output file.
- Apr 12, 2020 root@centos8-1 # yum -y install openssl Step 2: OpenSSL encrypted data with salted password. When we create private key for Root CA certificate, we have an option to either use encryption for private key or create key without any encryption.
- Sep 12, 2014 Generate a CSR from an Existing Private Key. Use this method if you already have a private key that you would like to use to request a certificate from a CA. This command creates a new CSR (domain.csr) based on an existing private key (domain.key): openssl req -key domain.key -new -out domain.csr.
1. Log in to your server’s terminal.
You will want to log in via Secure Shell (SSH).
2. Enter CSR and Private Key command
Generate a private key and CSR by running the following command:

Here is the plain text version to copy and paste into your terminal:
Note:Replace “server ” with the domain name you intend to secure.
3. Enter your CSR details
Enter the following CSR details when prompted:
- Common Name: The FQDN (fully-qualified domain name) you want to secure with the certificate such as www.google.com, secure.website.org, *.domain.net, etc.
- Organization: The full legal name of your organization including the corporate identifier.
- Organization Unit (OU): Your department such as ‘Information Technology’ or ‘Website Security.’
- City or Locality: The locality or city where your organization is legally incorporated. Do not abbreviate.
- State or Province: The state or province where your organization is legally incorporated. Do not abbreviate.
- Country: The official two-letter country code (i.e. US, CH) where your organization is legally incorporated.
Note: You are not required to enter a password or passphrase. This optional field is for applying additional security to your key pair.
4. Generate the order
Locate and open the newly created CSR in a text editor such as Notepad and copy all the text including:
Note 1: Your CSR should be saved in the same user directory that you SSH into unless otherwise specified by you.
Note 2: We recommend saving or backing up your newly generate “.key ” file as this will be required later during the installation process.
Return to the Generation Form on our website and paste the entire CSR into the blank text box and continue with completing the generation process.
Upon generating your CSR, your order will enter the validation process with the issuing Certificate Authority (CA) and require the certificate requester to complete some form of validation depending on the certificate purchased. For information regarding the different levels of the validation process and how to satisfy the industry requirements, reference our validation articles.
After you complete the validation process and receive the trusted SSL Certificate from the issuing Certificate Authority (CA), proceed with the next step using our SSL Installation Instructions for Nginx using OpenSSL.
Was this article helpful?
Related Articles
While Encrypting a File with a Password from the Command Line using OpenSSLis very useful in its own right, the real power of the OpenSSL library is itsability to support the use of public key cryptograph for encrypting orvalidating data in an unattended manner (where the password is not required toencrypt) is done with public keys.
The Commands to Run
Generate a 2048 bit RSA Key
You can generate a public and private RSA key pair like this:
openssl genrsa -des3 -out private.pem 2048
That generates a 2048-bit RSA key pair, encrypts them with a password you provideand writes them to a file. You need to next extract the public key file. You willuse this, for instance, on your web server to encrypt content so that it canonly be read with the private key.
Export the RSA Public Key to a File
This is a command that is
openssl rsa -in private.pem -outform PEM -pubout -out public.pem
The -pubout flag is really important. Be sure to include it.
Next open the public.pem and ensure that it starts with-----BEGIN PUBLIC KEY-----. This is how you know that this file is thepublic key of the pair and not a private key.
To check the file from the command line you can use the less command, like this:
less public.pem
Do Not Run This, it Exports the Private Key
A previous version of the post gave this example in error.
openssl rsa -in private.pem -out private_unencrypted.pem -outform PEM
The error is that the -pubout was dropped from the end of the command.That changes the meaning of the command from that of exporting the public keyto exporting the private key outside of its encrypted wrapper. Inspecting theoutput file, in this case private_unencrypted.pem clearly shows that the keyis a RSA private key as it starts with -----BEGIN RSA PRIVATE KEY-----.
Visually Inspect Your Key Files
It is important to visually inspect you private and public key files to makesure that they are what you expect. OpenSSL will clearly explain the nature ofthe key block with a -----BEGIN RSA PRIVATE KEY----- or -----BEGIN PUBLIC KEY-----.
You can use less to inspect each of your two files in turn:
less private.pemto verify that it starts with a-----BEGIN RSA PRIVATE KEY-----less public.pemto verify that it starts with a-----BEGIN PUBLIC KEY-----
The next section shows a full example of what each key file should look like.
The Generated Key Files
The generated files are base64-encoded encryption keys in plain text format.If you select a password for your private key, its file will be encrypted withyour password. Be sure to remember this password or the key pair becomes useless.
The private.pem file looks something like this:
The public key, public.pem, file looks like:
Protecting Your Keys
Depending on the nature of the information you will protect, it’s important tokeep the private key backed up and secret. The public key can be distributedanywhere or embedded in your web application scripts, such as in your PHP,Ruby, or other scripts. Again, backup your keys!
Remember, if the key goes away the data encrypted to it is gone. Keeping aprinted copy of the key material in a sealed envelope in a bank safety depositbox is a good way to protect important keys against loss due to fire or harddrive failure.
Oh, and one last thing.
If you, dear reader, were planning any funny business with the private key that I have just published here. Know that they were made especially for this series of blog posts. I do not use them for anything else.
Found an issue?
Rietta plans, develops, and maintains applications.
Openssl Generate Private Key No Password Code
Learn more about our services or drop us your email and we'll e-mail you back.