Methods For Generating Exchnange Or Distribute Keys
The worst that will happen is that they will say no (well ok.they could ban you from all NCSfot games technically.but there not going to do that for asking a simple question:P). But you can always ask support to see what they can do. There is no offical way of doing this and offically you cant do it.keys are a one time activation thing. Guild wars factions access key generator reviews. Assuming you cant transfer it (and seriously.dont get your hopes up opn that).if you have your brothers login details then you can juse use his accounts.
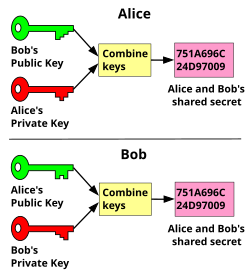
In symmetric key cryptography, both parties must possess a secret key which they must exchange prior to using any encryption. Distribution of secret keys has been problematic until recently, because it involved face-to-face meeting, use of a trusted courier, or sending the key through an existing encryption channel. The first two are often impractical and always unsafe, while the third depends on the security of a previous key exchange.
You are concerned about the strength of your cryptographic keys, so you implement a system that does the following:. The initial key is fed into the input of the bcrypt utility on a Linux workstation. The bcrypt utility produces an enhanced key that is 128 bits long. Especially if public key authentication is not set up yet, every scp. Stack Exchange Network. Stack Exchange network consists of 175 Q&A communities including Stack Overflow, the largest, most trusted online community for developers to learn, share. Best way to distribute user's public SSH key to many hosts? Ask Question Asked 2 years, 5.
In public key cryptography, the key distribution of public keys is done through public key servers. When a person creates a key-pair, they keep one key private and the other, known as the public-key, is uploaded to a server where it can be accessed by anyone to send the user a private, encrypted, message..
Secure Sockets Layer (SSL) uses Diffie–Hellman key exchange if the client does not have a public-private key pair and a published certificate in the public key infrastructure, and Public Key Cryptography if the user does have both the keys and the credential.
Jun 09, 2016.For an introduction to these features, please refer to Bluetooth Pairing Part 1: Pairing Feature Exchange. After this exchange, both devices can select which key generation method is used in subsequent phases. Here is the list of key generation methods for Bluetooth LE legacy pairing and Bluetooth LE Secure Connection. Bluetooth LE Legacy Pairing. Start studying Chapter 14, 15, and 16. Learn vocabulary, terms, and more with flashcards, games, and other study tools. This strategy involves the use of a trusted key distribution center (KDC). Each party in the network shares a secret key, known as a master key, with the KDC. The KDC is responsible for generating keys to be used for a. Distribution keys and collocated joins Dynamic redistribution or broadcasts If your database design or data distribution precludes you from distributing certain tables on the join key (column), the IBM Netezza system dynamically redistributes or broadcasts the required data.
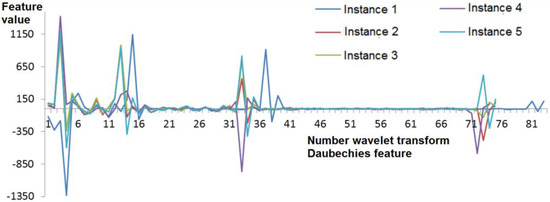
Key distribution is an important issue in wireless sensor network (WSN) design. There are many key distribution schemes in the literature that are designed to maintain an easy and at the same time secure communication among sensor nodes. The most accepted method of key distribution in WSNs is key predistribution, where secret keys are placed in sensor nodes before deployment. When the nodes are deployed over the target area, the secret keys are used to create the network.[1]For more info see: key distribution in wireless sensor networks.
Storage of keys in the cloud[edit]
Key distribution and key storage are more problematic in the cloud due to the transitory nature of the agents on it.[2]Secret sharing can be used to store keys at many different servers on the cloud.[3] In secret sharing, a secret is used as a seed to generate a number of distinct secrets, and the pieces are distributed so that some subset of the recipients can jointly authenticate themselves and use the secret information without learning what it is. But rather than store files on different servers, the key is parceled out and its secret shares stored at multiple locations in a manner that a subset of the shares can regenerate the key.
Secret sharing is used in cases where one wishes to distribute a secret among N shares so that M < N of them (M of N) can regenerate the original secret, but no smaller group up to M − 1 can do so.[4][5]
Notes[edit]
- ^Du, Wenliang Kevin; Deng, Jing; Han, Yunghsiang S.; and Varshney, Pramod K., 'A Pairwise Key Pre-Distribution Scheme for Wireless Sensor Networks' (2000). Electrical Engineering and Computer Science. Paper 36.http://surface.syr.edu/eecs/36
- ^Yu, S. et al. Achieving Secure, Scalable, and Fine-grained Data Access Control in Cloud Computing. IEEE INFOCOM 2010.
- ^Parakh, A. and Kak, S. Online data storage using implicit security. Information Sciences, vol. 179, pp. 3323-3331, 2009.
- ^Shamir, Adi (1979). 'How to share a secret'. Communications of the ACM 22 (11): 612–613.
- ^Blakley, G. R. (1979). 'Safeguarding cryptographic keys'. Proceedings of the National Computer Conference 48: 313–317.